3 minutes
Crescendo

Prior to 2017, researchers couldn’t easily monitor actions performed by a process on macOS and had to resort to coding scripts that produced low level system call data. FireEye released Monitor.app in 2017 that enabled collection of information on macOS at a higher level; at a simplified data set versus something like Dtrace. I created many versions of Monitor.app over the years and have received very positive feedback from users. Recently though, users have noticed it doesn’t work on macOS Catalina (10.15)…
Originally, a kernel extension was required to provide the inspection capabilities offered by Monitor.app. Unfortunately, kernel extensions are running in privileged mode which has very little protection from software bugs that may lead to system instability. This means kernel extensions should only be used if absolutely necessary. Microsoft and Apple have started providing engineers more userland alternatives to accomplish what previously required writing kernel code.
In Catalina, Apple released the Endpoint Security Framework (ESF) to provide a robust and (more importantly) safer way of getting access to internal operating system artifacts. Being a security guy, I’m not a huge fan when apps must ship with kernel extension to get their job done and I think this is a move in the right direction. With the coming release of 10.15.4, Apple will now pop-up a warning when a kernel extension is loaded that uses a set of these deprecated kernel programming interfaces (KPI’s).
Now seemed like a good time to kick the tires on the Endpoint Security Framework. Also, what engineer doesn’t love to learn new languages, so why not write it all in Swift as well?
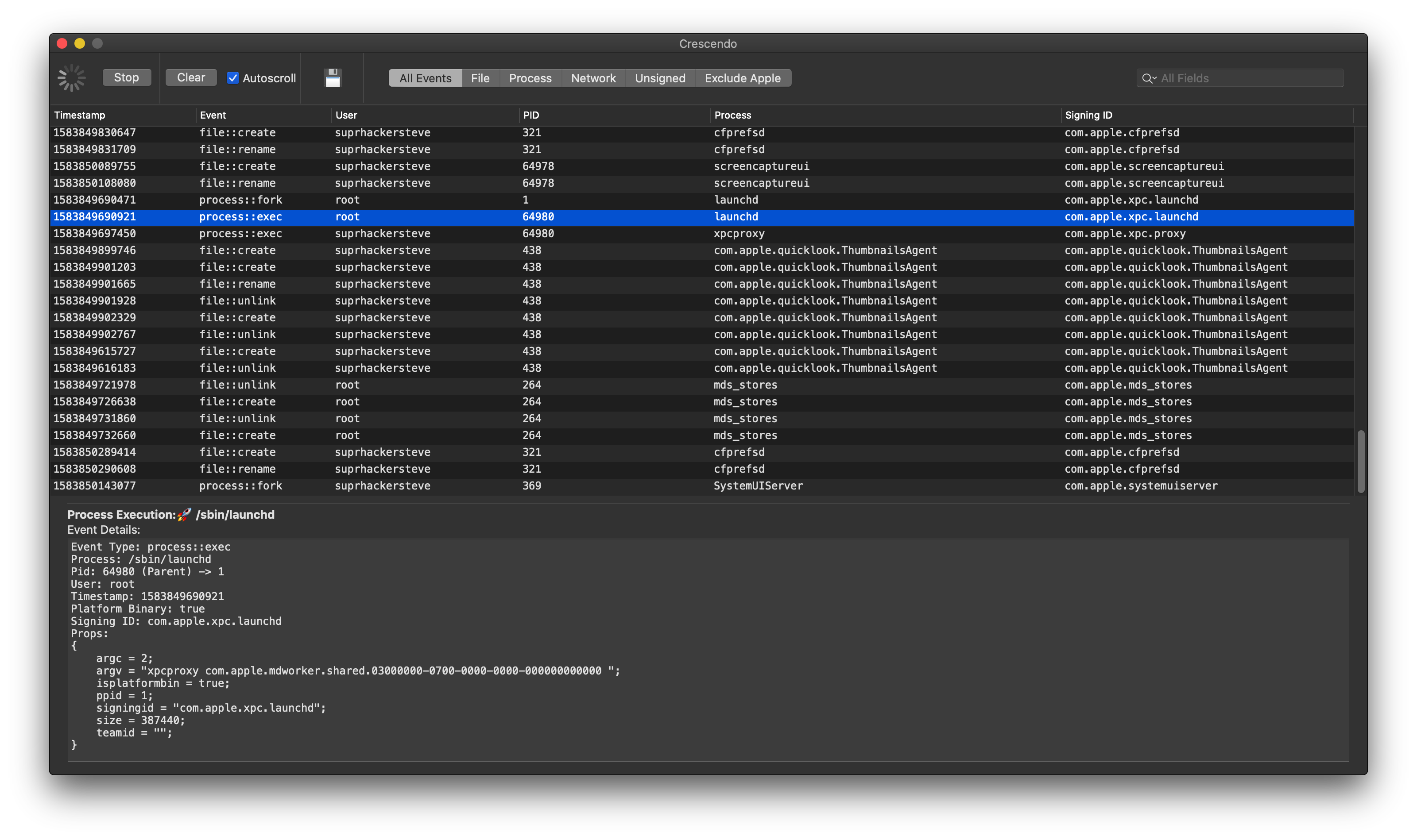
Crescendo is a real time event viewer for macOS that uses the ESF to show process executions and forks, file events, share mounting events, kernel extension loads, and IPC event data. ESF provides a vast amount of data, but the goal was to just pick out the things that analysts would be interested in when analyzing a piece of malware or trying to understand how a process (or component) works. Just the right amount of data without being a firehose of events to the user.
Features
- System Extension using Endpoint Security Framework
- Real time event viewer and event detail viewer
- Search for easy filtering of events by process, PID, username, or event type
- Filters for unsigned apps vs apple signed apps
- Ability to export all events to JSON
- Context highlighting when unsigned apps are executed
Apple has added some extra security features that require some extra setup for enabling Crescendo’s system extension. Head on over to the Getting Started section in the README to get started. I’m hopeful this inconvenience will be fixed in future versions.
Oh, one more thing…
Crescendo is being released open source under the MIT license! It consists of a ready to use framework that wraps the ESF with a Swift interface, removing some of the nuances and providing a simple callback for event data. This way other developers don’t have to understand all the inner details of the Endpoint Security Framework. One caveat, if you wish to use the framework in your own app, you must obtain an entitlement from Apple.
Missing a feature you’d like to see? Submit a Pull Request!